A2A External Agent Interoperability.
Open the conductor ecosystem to external agents. Enable Google A2A protocol compliance, MCP bridge connectivity, and REST API access — all governed by trust levels, rate limits, and the same governance framework that controls internal agents. 38 agents, no longer a closed loop.
Problem Statement
The conductor ecosystem operates 38 agents in a closed communication loop. Agents dispatch to each other via the Task tool, validated by Gemini, governed by the approval framework — but this entire system is invisible to the outside world. No external agent can participate, and no internal agent can advertise its capabilities externally.
Multi-platform orchestration already happens in practice: Claude Code agents invoke Gemini CLI for validation, Codex CLI for secondary review, and shell scripts for infrastructure tasks. But this integration is ad-hoc shell scripting — no standard protocol, no authentication, no capability discovery, no governance enforcement.
Closed Agent Loop
38 agents communicate exclusively through internal Task tool dispatch. An external Gemini agent, a Codex agent, or a custom n8n workflow cannot invoke conductor capabilities or participate in orchestrated workflows.
No Capability Advertisement
Internal agents have well-defined capabilities (in capabilities.yaml), but this information is not machine-readable by external systems. No Agent Cards, no discovery endpoint, no standardized capability schema.
Ad-hoc Multi-Platform Integration
Gemini validation uses shell-exec to invoke gemini CLI. This works but lacks error handling, retry logic, authentication, rate limiting, and governance audit trails that formal protocol integration would provide.
No Trust Model for External Agents
Internal agents have trust levels in capabilities.yaml (advisory, standard, privileged). External agents have no trust classification. A Telegram bot and a locally-running Gemini instance receive the same (zero) level of trust.
No Context Sharing Protocol
When an external agent is invoked, context is passed as unstructured text. There is no envelope format that carries governance metadata, session context, or provenance information alongside the task payload.
No Audit Trail for External Invocations
Internal agent dispatches are tracked in conductor-state.json and validated by Gemini. External invocations bypass both systems entirely, creating a governance blind spot.
Architecture
The Agent Gateway sits between the conductor ecosystem and the external world. It exposes a unified HTTP interface that routes requests through protocol-specific adapters (A2A, MCP, REST) to internal agents. Every request passes through authentication, rate limiting, and governance checks before reaching any agent.
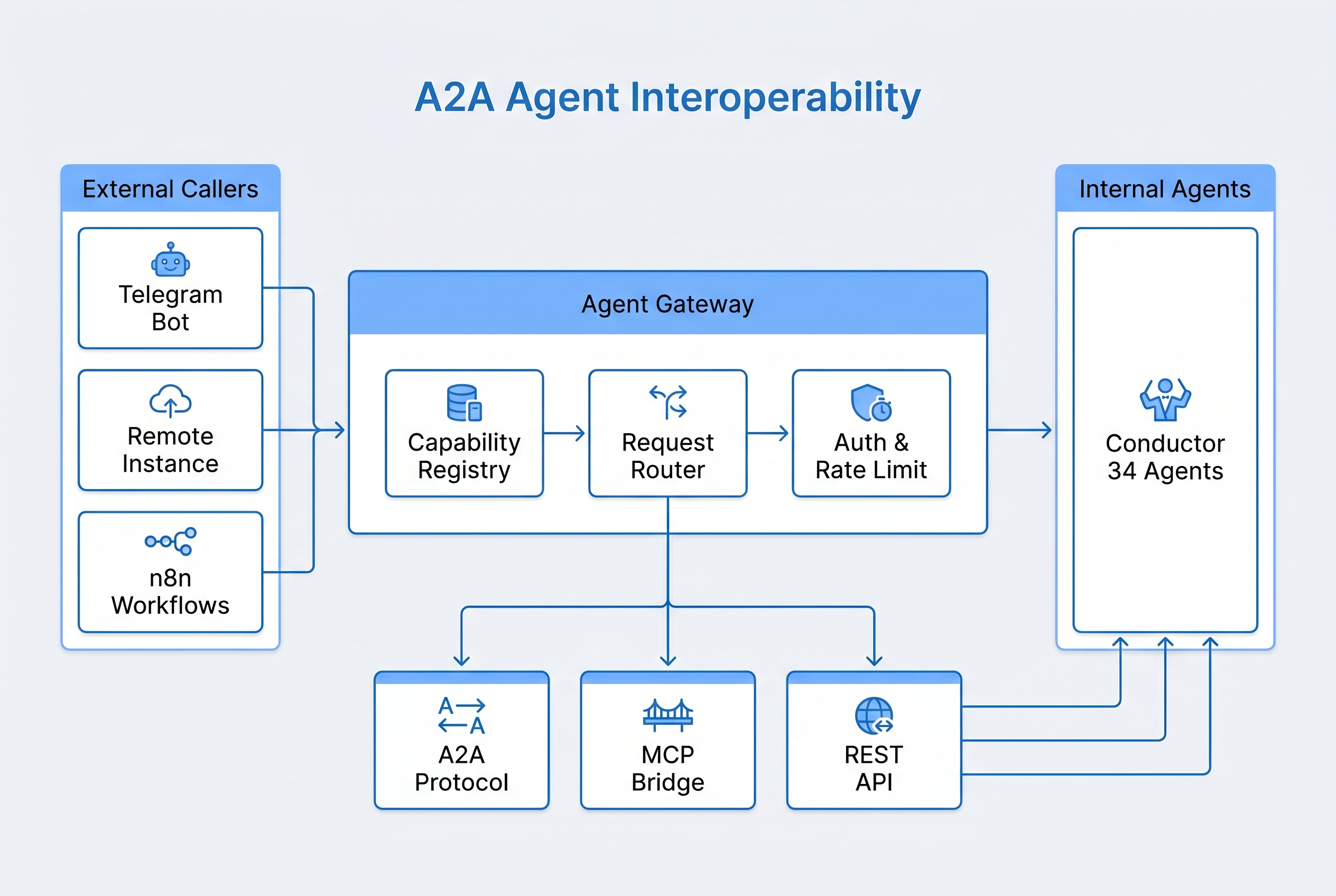
Single Gateway, Multiple Protocols
All external access flows through one FastAPI gateway. Protocol-specific adapters translate between A2A, MCP, and REST formats and the internal dispatch format. This provides a single point for authentication, rate limiting, and audit logging.
Selective Exposure
Only 15 of 38 agents are externally callable. The orchestrator (conductor), state management (conductor-checkpoint), and security-sensitive agents (conductor-ciso, conductor-pentest-coordinator) remain internal-only.
Governance-First Design
Every external request is wrapped in a context envelope carrying governance metadata. The same approval gates and audit trails that govern internal dispatch apply to external invocations. No governance bypass.
Key Components
Protocol Adapters
A2A Protocol Adapter
Full compliance with Google's A2A specification. Enables conductor agents to interoperate with any A2A-compliant agent ecosystem. Publishes Agent Cards for the 15 externally-callable agents with standardized capability descriptions, input/output schemas, and authentication requirements.
- Agent Card generation from capabilities.yaml
- Task lifecycle management (submit, status, result, cancel)
- Streaming support for long-running agent tasks
- Push notification webhooks for async completion
MCP Bridge
Exposes conductor agent capabilities as MCP tools, enabling any Claude Code instance to invoke conductor agents as if they were local MCP server tools. This is the primary integration path for multi-instance Claude Code deployments where a remote conductor serves as a shared orchestration backend.
- Each exposed agent becomes an MCP tool with typed parameters
- Tool list endpoint for automatic discovery
- SSE transport for real-time result streaming
- Context passing via MCP tool parameters
REST API Adapter
Simple HTTP/JSON interface for non-agent callers: shell scripts, n8n workflows, Telegram bots, CI/CD pipelines, and monitoring systems. Three endpoints cover the full lifecycle: invoke, status, and result.
POST /api/v1/invoke/{agent}— dispatch a taskGET /api/v1/status/{task_id}— check task statusGET /api/v1/result/{task_id}— retrieve completed result- API key authentication with per-key trust level assignment
Trust Levels
Five trust levels govern what external callers can access. Trust level determines which agents are callable, which operations are permitted, and what rate limits apply.
Supporting Components
Agent Capability Registry
YAML-based registry (extending capabilities.yaml) with machine-readable schemas for all 38 agents. Marks 15 as externally callable. Published via HTTP discovery endpoint, A2A Agent Cards, and MCP tool list.
Context Sharing Protocol
Standardized envelope format wrapping every cross-boundary request. Carries: task payload, governance metadata (session ID, trust level, approval chain), provenance (caller identity, protocol, timestamp), and response routing.
Agent Discovery
Four discovery mechanisms: static YAML registry (local), HTTP endpoint (remote), A2A Agent Cards (Google ecosystem), and MCP tool list (Claude Code ecosystem). All derive from the same source of truth.
Gateway Health & Metrics
Exposes /health endpoint for monitoring. Tracks requests per protocol, response latency, error rates, trust level distribution, and rate limit rejections. Feeds into Memory Dashboard (PRD 6).
Requirements
| ID | Requirement | Priority |
|---|---|---|
| REQ-A2A-001 | Agent Gateway SHALL expose a FastAPI-based HTTP interface supporting A2A Protocol, MCP Bridge, and REST API protocol adapters on a configurable port (default 8420). | MUST |
| REQ-A2A-002 | Agent Capability Registry SHALL define machine-readable capability schemas for all 38 agents, with an externally_callable flag marking exactly 15 agents as accessible via the gateway. |
MUST |
| REQ-A2A-003 | A2A Protocol Adapter SHALL implement Google A2A specification including Agent Card publication, task lifecycle management (submit/status/result/cancel), and streaming support for long-running tasks. | MUST |
| REQ-A2A-004 | MCP Bridge SHALL expose each externally-callable agent as an MCP tool with typed parameters, supporting SSE transport for real-time result streaming and automatic tool discovery. | MUST |
| REQ-A2A-005 | REST API Adapter SHALL provide three endpoints (POST /invoke/{agent}, GET /status/{task_id}, GET /result/{task_id}) with JSON request/response format and API key authentication. |
MUST |
| REQ-A2A-006 | Authentication system SHALL enforce 5 trust levels (local=5, remote=4, bot/n8n=3, external=2, unknown=0) with per-level access control determining callable agents and permitted operations. | MUST |
| REQ-A2A-007 | Every external invocation SHALL be wrapped in a Context Sharing Protocol envelope carrying task payload, governance metadata (session ID, trust level, approval chain), and provenance (caller identity, protocol, timestamp). | MUST |
| REQ-A2A-008 | Rate limiting SHALL be enforced per trust level with configurable thresholds (default: local=unlimited, remote=100/min, bot=30/min, external=10/min, unknown=discovery only). | MUST |
| REQ-A2A-009 | All external invocations SHALL be logged to the governance audit trail (PRD 5) with the same event structure used for internal agent dispatches, including trust level and protocol used. | MUST |
| REQ-A2A-010 | Agent Discovery SHALL support four mechanisms: static YAML registry, HTTP discovery endpoint, A2A Agent Cards, and MCP tool list — all derived from the same source of truth (capabilities.yaml). | SHOULD |
| REQ-A2A-011 | Gateway SHALL support async-first invocation: all task dispatches return immediately with a task_id, with result retrieval via polling or webhook notification. | MUST |
| REQ-A2A-012 | System SHALL degrade gracefully when the gateway is unavailable: internal agent dispatch MUST continue functioning, and a standalone script fallback SHALL enable direct agent invocation without the gateway. | MUST |
| REQ-A2A-013 | Gateway health endpoint (/health) SHALL report gateway status, protocol adapter availability, active connections per protocol, and request metrics (latency, error rate, trust level distribution). |
SHOULD |
| REQ-A2A-014 | External invocations from trust levels 2 and below SHALL be subject to the same governance approval gates as internal agent dispatches, with no bypass mechanism. | MUST |
| REQ-A2A-015 | Agent Economics (PRD 10) integration SHALL track cost attribution for externally-invoked tasks, including protocol overhead, with per-caller cost reporting. | SHOULD |
| REQ-A2A-016 | System SHALL support bidirectional interop: internal agents can invoke external A2A-compliant agents and MCP servers through the same gateway, subject to the same trust and governance controls. | COULD |
Design Decisions
Key architectural and design choices, with rationale for each decision.
- Only 15 of 38 agents exposed externally. The orchestrator (conductor), state management (conductor-checkpoint), security agents (conductor-ciso, conductor-pentest-coordinator), and the Gemini validator are internal-only. Exposing orchestration control to external callers would create a privilege escalation path. The 15 exposed agents are functional workers (builder, architect, QA, doc-gen) that produce bounded outputs.
- Async-first invocation model. Agent tasks can take seconds to minutes. Synchronous HTTP request/response would require long-lived connections and risk timeouts. Async dispatch (return task_id immediately, poll or webhook for result) is more resilient, enables queuing, and matches the existing conductor dispatch model.
- Three protocol adapters, not one. A2A serves the Google agent ecosystem. MCP Bridge serves the Claude Code ecosystem. REST serves everything else (scripts, bots, CI/CD). Forcing all callers through A2A would exclude non-Google agents; forcing all through REST would lose the rich capability discovery and streaming that A2A and MCP provide.
- Governance metadata in the context envelope, not out-of-band. Every external request carries governance metadata (trust level, session ID, approval chain) inside the request envelope rather than in HTTP headers or a separate governance channel. This ensures governance travels with the request through any intermediary and cannot be accidentally stripped.
- Standalone script fallback for gateway unavailability. If the FastAPI gateway is down, internal operations must continue. The standalone fallback enables direct agent invocation via shell scripts (the current approach), ensuring the gateway is an enhancement, not a single point of failure.
- FastAPI as the gateway framework. Python with FastAPI provides: async support (essential for agent dispatch), automatic OpenAPI schema generation (free documentation), middleware for auth/rate-limiting, and compatibility with the existing Python tooling in the ecosystem. Performance is adequate for the expected request volume (hundreds/day, not thousands/second).
- YAML registry as single source of truth. Agent capabilities are defined once in YAML (extending the existing capabilities.yaml). All four discovery mechanisms (static, HTTP, A2A Cards, MCP tools) derive from this single source. No capability can be advertised externally that is not defined in the registry.
Integration Map
A2A Interoperability connects to 10 systems, serving as the boundary layer between the conductor ecosystem and the external world.
| Integration | Direction | Data Exchanged |
|---|---|---|
| Conductor (PRD 2) | Dispatches to | Routes externally-received requests to internal agent dispatch. Receives task results for return to external callers. Extends the Task tool dispatch model to gateway-initiated requests. |
| Governance (PRD 5) | Enforces / Logs | All external invocations pass through governance approval gates. Audit events logged with trust level, protocol, caller identity. Same gate enforcement as internal dispatch — no bypass. |
| Runtime Security (PRD 11) | Enforces | Request validation, input sanitization, and threat detection for all external requests. Rate limiting enforcement. Trust level verification against authentication tokens. |
| Agent Economics (PRD 10) | Reports to | Cost attribution for externally-invoked tasks, including protocol overhead. Per-caller cost tracking enables chargeback for shared infrastructure. |
| Memory System (PRD 4) | Reads / Writes | Reads capability registry and agent metadata. Writes external interaction patterns for cross-session learning about external caller behavior. |
| Standalone Scripts | Fallback | Direct agent invocation via shell when gateway is unavailable. Ensures zero-downtime degradation for internal operations. |
| Telegram Bot | REST client | Invokes conductor agents via REST API adapter. Trust level 3 (bot). Primary use case: quick agent queries from mobile. |
| Remote Instances | A2A / MCP | Remote Claude Code or Gemini instances invoke conductor agents via A2A or MCP Bridge. Trust level 4 (remote) for authenticated instances. |
| n8n Workflows | REST client | n8n workflows invoke conductor agents via REST API for automated pipeline tasks. Trust level 3 (n8n). Enables CI/CD integration and scheduled agent tasks. |
| Event-Driven (PRD 13) | Publishes | Publishes gateway events (invocation received, task dispatched, result returned, auth failure, rate limit hit) to the event bus for monitoring and alerting. |
Prompt to Build It
Copy and paste this prompt into Claude Code to begin implementing A2A External Agent Interoperability. It references the architecture, protocols, and integration points defined in this PRD.
Build the A2A External Agent Interoperability system (PRD 17) for the
conductor plugin ecosystem.
## Context
38 agents operate in a closed loop. No external agents can participate,
no internal capabilities are advertised externally, and multi-platform
orchestration (Claude + Gemini + Codex) uses ad-hoc shell scripting.
## Architecture
Agent Gateway (FastAPI) with three protocol adapters:
- A2A Protocol Adapter: Google A2A spec compliance, Agent Cards, task
lifecycle (submit/status/result/cancel), streaming, push notifications
- MCP Bridge: expose agents as MCP tools, SSE transport, auto-discovery
- REST API: POST /invoke/{agent}, GET /status/{task_id}, GET /result/{task_id}
## Agent Exposure
- 38 total agents, 15 externally callable
- Internal-only: conductor, conductor-checkpoint, conductor-ciso,
conductor-pentest-coordinator, conductor-gemini-validator, and others
that control orchestration or security
- Exposed: builder, architect, QA, doc-gen, code-reviewer, and other
functional worker agents
## Trust Levels (5-tier authentication)
- Level 5 (local): same-machine, full access, unlimited rate
- Level 4 (remote): authenticated remote, full access, 100 req/min
- Level 3 (bot/n8n): API key auth, limited write, 30 req/min
- Level 2 (external): third-party A2A, advisory agents only, 10 req/min
- Level 0 (unknown): discovery endpoint only, no invocation
## Context Sharing Protocol
Standardized envelope for every cross-boundary request:
- Task payload (agent name, parameters, expected output)
- Governance metadata (session ID, trust level, approval chain)
- Provenance (caller identity, protocol, timestamp)
- Response routing (callback URL or poll configuration)
## Agent Discovery (4 mechanisms, 1 source of truth)
1. Static YAML registry (local file)
2. HTTP discovery endpoint (GET /api/v1/agents)
3. A2A Agent Cards (Google ecosystem)
4. MCP tool list (Claude Code ecosystem)
All derive from capabilities.yaml — single source of truth.
## Key Constraints
- Async-first: all invocations return task_id immediately
- Governance enforced on ALL external requests (same gates as internal)
- Standalone script fallback when gateway is unavailable
- FastAPI framework, configurable port (default 8420)
- All invocations logged to governance audit trail
- No governance bypass for any trust level
## Integration Points
- Dispatches to: Conductor (PRD 2)
- Enforces: Governance (PRD 5), Runtime Security (PRD 11)
- Reports: Agent Economics (PRD 10)
- Reads/Writes: Memory System (PRD 4)
- Publishes: Event-Driven (PRD 13)
- Clients: Telegram Bot, n8n workflows, remote instances
## Requirements
16 requirements (REQ-A2A-001 through REQ-A2A-016). MUST-priority items
are non-negotiable: FastAPI gateway, capability registry, A2A adapter,
MCP Bridge, REST API, trust levels, context envelopes, rate limiting,
governance audit, async dispatch, graceful degradation, and governance
enforcement for external callers.